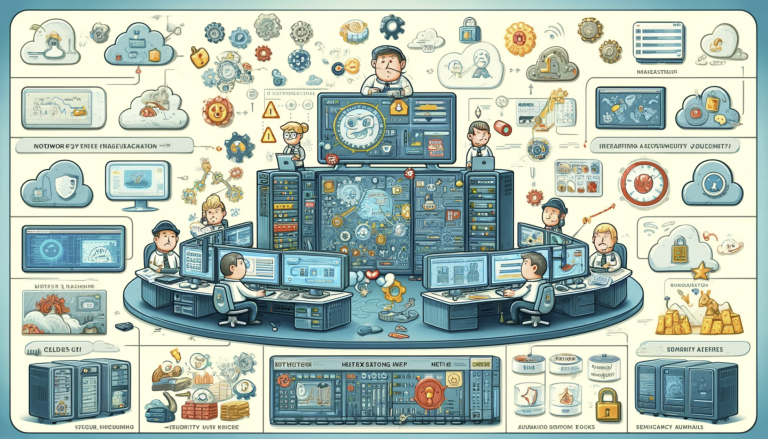
Network Management Best Practices: Optimizing Performance And Security
In the digital age, businesses rely heavily on their networks to function efficiently. However, managing and maintaining a complex network can be a daunting task. By implementing effective network management best practices, organizations can ensure optimal performance, enhance security, and minimize downtime.